TL;DR
Login history is an authentication log that records every login attempt to a Plutio workspace, capturing the IP address, geographic location, device details, browser user agent string, and exact timestamp for each session.
Plutio records both successful and failed login attempts in the authentication log, so workspace owners can identify unauthorized access attempts, audit team member activity, and trace sessions back to specific devices and locations. Over 35% of Plutio workspaces with 3+ team members review login history monthly to verify that access patterns match expected behavior. The critical detail: failed login attempts appear alongside successful ones, so a burst of failed password entries from an unfamiliar IP address in Lagos or Bucharest surfaces immediately, not after a breach.
Login history comes with all Plutio plans starting at $19/month, with a 7-day free trial. The authentication log starts recording automatically from the first login, with no setup or configuration needed.
What login history is
Login history is a chronological record of every authentication attempt against a Plutio workspace, storing the IP address, geo-IP location (city and country), device type, operating system, browser name and version, full user agent string, Meteor connection ID, and session metadata for each entry.
Every time someone enters credentials on a Plutio login screen, the authentication log creates a new record. The record captures whether the attempt succeeded or failed, which user account was targeted, the IP address the request came from, and the device and browser details extracted from the user agent string. Failed attempts from incorrect passwords or expired 2FA codes appear with the same level of detail as successful logins.
IP address and geographic tracking
Each authentication log entry includes the originating IP address and a geo-IP lookup that maps the IP to a city and country. A freelancer who works from Austin, Texas, can immediately spot a login attempt from Kyiv, Ukraine, without parsing raw IP addresses manually. Geographic tracking turns a wall of IP addresses into actionable location data that answers the question: did this login come from somewhere expected?
Device and user agent logging
Beyond location, each entry records the device type (desktop, mobile, tablet), operating system (macOS, Windows, iOS, Android), browser name and version (Chrome 122, Safari 17.3), and the full user agent string. A workspace owner reviewing the log can tell whether a login happened from a recognized MacBook Pro running Chrome or an unfamiliar Android device running an outdated browser. The user agent string is the forensic fingerprint of each session: it reveals not just what browser was used, but what OS version, what rendering engine, and whether the request came from a real browser or an automated script.
After a contractor left our team, login history showed us exactly when their last session ended and that no access attempts happened after we removed their account. The audit trail gave our client the documentation they needed.
Why login history matters for freelancers and agencies
Without an authentication log, a compromised password produces zero visibility into who accessed the workspace, what they saw, or how long the session lasted. A freelancer managing 10+ client projects in one workspace has contracts, invoices, bank details, and project files all behind a single login. One compromised credential exposes everything, and without login records the breach timeline stays invisible.
The cost is not abstract. A 2024 IBM Cost of a Data Breach report found that businesses with fewer than 500 employees averaged $3.31 million per breach, with credential theft as the most common initial attack vector at 16% of all breaches. Freelancers and small agencies carry that same credential risk with far fewer resources to recover. A client whose contract terms, payment history, or project files get exposed does not care whether the breach happened at a Fortune 500 company or a 3-person design studio.
Dubsado stores client data and contracts but offers no authentication log or login history feature in its workspace settings. A workspace owner on Dubsado who suspects unauthorized access has no built-in way to check which IP addresses connected, which devices were used, or whether failed login attempts occurred. The only option is to change the password and hope the problem stops.
The most dangerous breach is the one that goes undetected. Login history does not prevent unauthorized access on its own, but paired with two-factor authentication, login records turn a silent breach into a visible event with a timestamp, location, and device fingerprint attached.
Plutio's authentication log records every attempt automatically from the first login. Failed attempts surface immediately, so a pattern of 15 failed password entries from an IP address in a country where no team member operates becomes visible before an attacker gets through.
How login history works in Plutio
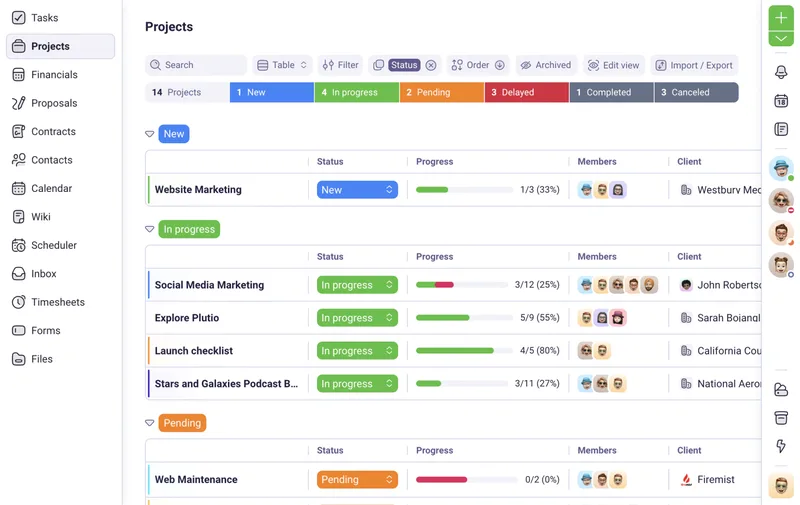
Plutio records every authentication attempt automatically with no configuration required, and workspace owners can review the full log filtered by user, date range, status, and IP address.
The authentication log starts recording from the first login to a workspace. Every login attempt, whether through email and password, two-factor authentication with TOTP codes, or SSO through Auth0, creates an entry in the log.
Step by step
- Step 1: Open the workspace settings in Plutio. Navigate to the authentication log section where all login records are stored chronologically.
- Step 2: Review the log entries. Each entry shows the user account, timestamp, login status (success or failure), IP address, geographic location (city and country), device type, operating system, browser, and full user agent string.
- Step 3: Filter entries by specific team member, date range, or login status to narrow down to the records that matter. Investigating a suspected breach means filtering for failed attempts first.
- Step 4: Cross-reference unfamiliar IP addresses or device fingerprints against known team member locations and devices. A login from a new city or an unrecognized browser version stands out immediately.
- Step 5: Take action based on findings. If an unauthorized login is confirmed, change the affected user's password, enable two-factor authentication if not already active, and review which projects and client data the session could have accessed.
Practical tip: combine login history with two-factor authentication. 2FA prevents unauthorized access; login history confirms that prevention worked. Together, they create both the lock and the record of who tried the door.
Who needs login history
Freelancers and agencies handling client contracts, financial records, and project files in a shared workspace need authentication logging to verify who accessed what, when, and from where.
A freelance accountant managing tax documents and bank details for 15+ clients needs to demonstrate that only authorized personnel accessed those records. Login history provides the audit trail: every session has a timestamp, IP address, and device fingerprint attached. When a client asks who has accessed their financial data in the last 90 days, the authentication log answers the question in minutes rather than guesswork.
Agencies with 5+ team members, contractors, and client collaborators face a different scale of the same problem. A contractor who finishes a project should have their access removed, but without login history there is no way to confirm that the removal actually stopped all access. Plutio's authentication log shows the exact last login timestamp and confirms whether any access attempts happened after account removal, giving the agency documentation for client-facing compliance reports.
HoneyBook offers a team activity log for internal actions but does not provide IP address tracking, geographic location data, or failed login attempt records in its workspace settings. Freelancers switching from HoneyBook who need device-level login auditing find that Plutio's authentication log covers the forensic details that activity logs miss: not just what someone did inside the app, but how they got in, from where, and with what device.
| Feature | Plutio | HoneyBook |
|---|---|---|
| Login attempt logging | Yes, all attempts | No |
| IP address tracking | Yes | No |
| Geographic location | Yes, city and country | No |
| Device and browser details | Yes, full user agent | No |
| Failed login recording | Yes | No |
| SSO support | Yes, Auth0 | Yes, Google SSO |
Bottom line: any freelancer or agency storing client-sensitive data, financial records, or signed contracts in a shared workspace needs login history to answer one question at any time: who logged in, from where, and was the access legitimate?