TL;DR
Role permissions in Plutio give every custom role a dedicated matrix of 100+ toggles covering view, create, edit, delete, send, and status-change access across projects, tasks, invoices, proposals, contracts, files, scheduling, automations, wiki, and more.
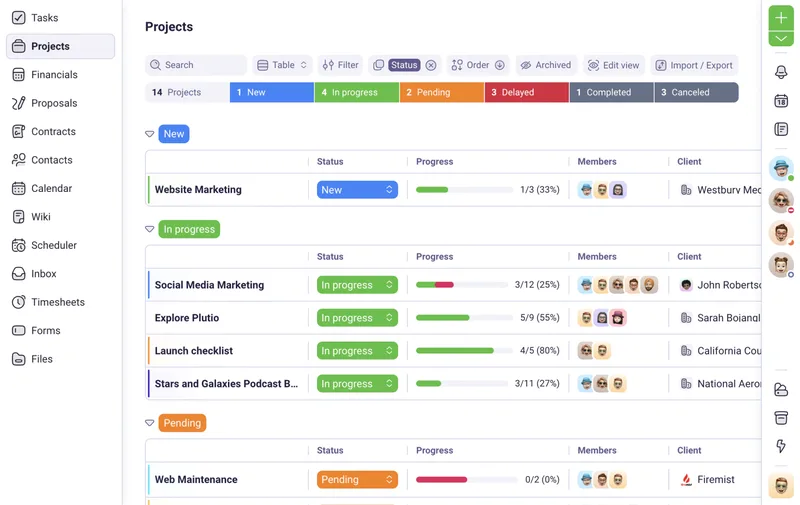
Plutio organizes permissions by module, so configuring a new role means walking through each category (Contacts, Projects, Task Boards, Tasks, Files, Financials, Proposals, Contracts, Forms, Timesheets, Schedulers, Automations, Inbox, Wiki, Templates, Trash, Archive, Custom Fields, and Snippets) and toggling individual actions on or off. Over 65% of Plutio teams on the Pro plan create at least one custom role within the first week of onboarding. The core advantage: permissions are granular enough to separate "can view invoices" from "can send invoices" and "can view billing rates" from "can edit billing rates," so access control matches actual job responsibilities instead of forcing a binary Admin-or-Member choice.
Permissions are managed in Settings under Permissions on the Pro plan ($49/month) and Max plan ($199/month). Changes apply instantly to every team member assigned to that role. The 7-day free trial includes full access to custom roles and all 100+ permission toggles.
What role permissions are
Role permissions are individual access controls assigned to a named role that determine exactly which actions a team member can perform within each module of a Plutio workspace.
Each permission is a binary toggle: on or off. When a team member is assigned a role, every toggle in that role's permission matrix applies to them immediately. Permissions don't cascade or inherit from other roles. The role assigned to a team member is the single source of truth for what they can and can't do. If a permission toggle is off, the corresponding action, button, or menu item becomes invisible to that team member, not just disabled but completely hidden from the interface.
Module-level permission categories
Permissions in Plutio are organized into 18+ module categories. Contacts covers viewing, creating, editing, and deleting people and companies. Projects includes viewing, creating, editing, deleting, managing members, managing permissions, viewing budgets, and managing task boards. Tasks breaks down into viewing, creating, completing, editing, commenting, delegating, and deleting. Financials splits into invoices (view, create, edit, send, delete), recurring billing, and transactions. Proposals and contracts each have their own view, create, edit, send, and delete toggles. Files separate into upload, edit, comment, and delete. Additional modules include Forms, Timesheets (with separate billing rate and cost rate visibility toggles), Schedulers, Automations, Inbox, Wiki, Templates, Trash, Archive, Custom Fields, and Snippets. Each module operates independently, so turning off Financials doesn't affect Projects or Files.
Action-level granularity within modules
Within each module, permissions go beyond basic CRUD (create, read, update, delete). Project permissions include "manage members" (control who joins a project), "manage permissions" (set entity-level overrides), and "view budgets" (see project budget data). Invoice permissions separate "view" from "send" and "edit," so a team member can view invoices without being able to email them to clients. Task permissions include "complete" (mark done), "delegate" (assign to others), and "comment" (add notes) as independent toggles. Timesheet permissions split "view billing rate" from "view cost rate," allowing a project manager to see billable hours without knowing internal cost data. The granularity means a 10-person agency can define a "Junior Designer" role that views projects and uploads files but can't delete files, edit task assignments, or see any financial module, all without writing a single line of code or contacting support.
We tried Asana and ClickUp before Plutio, but neither let us separate invoice viewing from invoice sending. In Plutio, our project managers can check if an invoice was sent without being able to email the next one. That level of control matters when billing $15K projects.
Why granular permissions matter for agencies and freelancers
Coarse permission models force a choice between giving a team member too much access or too little, and both options create operational problems that cost real money.
When a VA has full access to invoices because the tool only offers "Admin" and "Member" tiers, that VA can accidentally change a $5,000 invoice line item, delete a payment record, or send a draft invoice to a client before it's reviewed. When a contractor is restricted to "Member" access because there's no way to grant project access without exposing financial data, that contractor can't view task boards or upload deliverables, so every file exchange happens over email instead of inside the project workspace. On an agency running 15 active client projects, either scenario adds 2 to 5 hours of weekly overhead from manual workarounds, forwarded files, and damage control conversations.
Dubsado handles team access through a basic permissions model that separates forms, templates, workflows, and financials into broad categories, but individual action toggles (like "can view but not send invoices") are limited. A team member with financial access in Dubsado can view, edit, and send invoices without the option to restrict sending as a separate permission. HoneyBook limits its workspace roles to Owner, Team Member, and Bookkeeper on its Essentials plan, with custom permissions available only on the Premium plan at $39/month per user, which makes per-seat costs grow fast for agencies with 5+ people.
The real cost of insufficient access control isn't a security breach but the slow, constant friction of workarounds: sending files over email because the tool can't grant file access without exposing invoices, or manually reviewing every action because the permission model can't prevent the wrong ones.
Plutio eliminates that trade-off by splitting each module into individual action-level toggles. Granting project access doesn't mean granting invoice access. Granting invoice viewing doesn't mean granting invoice sending. The result is a permission model that matches how agencies actually delegate work: different people handle different responsibilities, and each person's access should reflect their actual job, not the closest available preset.
How role permissions work in Plutio
Open Settings, navigate to Permissions, select or create a role, and configure each module's permission toggles individually.
Role permission management requires Owner or Co-Owner access. Team members assigned to a role see only the modules and actions their role permits, everything else is hidden from their interface entirely.
Step by step
- Step 1: Go to Settings and select Permissions from the sidebar. All existing roles display in a list with their names and the number of team members assigned to each.
- Step 2: Click an existing role to edit its permissions, or click "Create" to add a new role. Enter a descriptive name like "Designer," "Bookkeeper," or "Project Manager."
- Step 3: Walk through each permission category. Expand Contacts to toggle view, create, edit, and delete for people and companies. Expand Projects to toggle view, create, edit, delete, manage members, manage permissions, view budgets, and manage task boards. Expand Tasks to toggle view, create, complete, edit, comment, delegate, and delete.
- Step 4: Configure financial permissions separately. Under Invoices, toggle view, create, edit, send, and delete independently. Under Timesheets, toggle view billing rate and view cost rate as separate switches. Turn off entire financial categories for roles that should never see pricing data.
- Step 5: Use the "View as" button to preview the workspace as that role sees it. The preview shows which sidebar items appear, which records are visible, and which action buttons are available. Adjust any toggles that show too much or too little access.
- Step 6: Assign team members to the role from People. Open a team member's profile, select the role from the dropdown, and the new permissions apply immediately. Optionally, customize the sidebar menu for the role in Settings under Main Menu to hide navigation items the role doesn't need.
Practical tip: create roles by job function (Designer, PM, Finance, VA) rather than by seniority level (Junior, Senior). Job-function roles map cleanly to module permissions and don't need updating when someone gets promoted.
Who needs granular role permissions
Any team with two or more people handling different responsibilities in a shared workspace needs granular permissions, but agencies billing $5,000+ per project and freelancers working with contractors on sensitive client data get the most immediate value.
A freelance consultant hiring a part-time VA to manage scheduling, inbox responses, and task updates needs that VA to access schedulers, inbox, and tasks without seeing proposals, contracts, or invoices. Without per-module permission control, the only options are full access (risky) or no access (useless), so the VA ends up working through email forwarding and screenshot sharing instead of inside the actual workspace. Granular permissions eliminate that workaround entirely: the VA gets a role with schedulers, inbox, and tasks turned on, and every financial and legal module turned off.
Agencies running 10+ concurrent client projects with designers, developers, project managers, and bookkeepers need each function to access different modules. A designer uploads files and views task boards. A developer accesses wiki documentation and project boards. A project manager views proposals, contracts, and project budgets. A bookkeeper manages invoices and transactions. In Plutio, each of those functions becomes a custom role with its own 100+ toggle permission set, and onboarding a new team member means assigning the role rather than configuring 50+ individual settings from scratch.
Teams comparing Dubsado alternatives often hit permission limitations first, since Dubsado doesn't separate "view invoice" from "send invoice" at the toggle level. Teams evaluating HoneyBook alternatives find that custom roles require HoneyBook's Premium plan at $39/month per user, which means a 6-person agency pays $234/month just for permission control before adding any other features. Plutio's Pro plan at $49/month (flat rate, not per seat) includes unlimited custom roles with all 100+ permission toggles.
Bottom line: granular permissions save 2 to 5 hours per week in manual workarounds on teams with 3+ people, because every team member accesses exactly what their job requires and nothing else.